Here is the continuation of password security. So you have a password manager, which has some serious advantages:
- You have secure passwords that are 12 to 20 characters long,
- made up of upper and lower case letters, numbers, and symbols
- are random(ish) by not containing dictionary words or their variants (like p@$$woRd)
- You can have a different password for every online account, stored away in an easy to use and retrieve format
You can also store answers to challenge questions in your wallet. When the bank challenges you to name your third grade teacher, you can respond with “Mrs. Smith” or you can answer the challenge with a random string of characters stored in your password wallet. Look at the “notes” field (not from my real account or wallet).
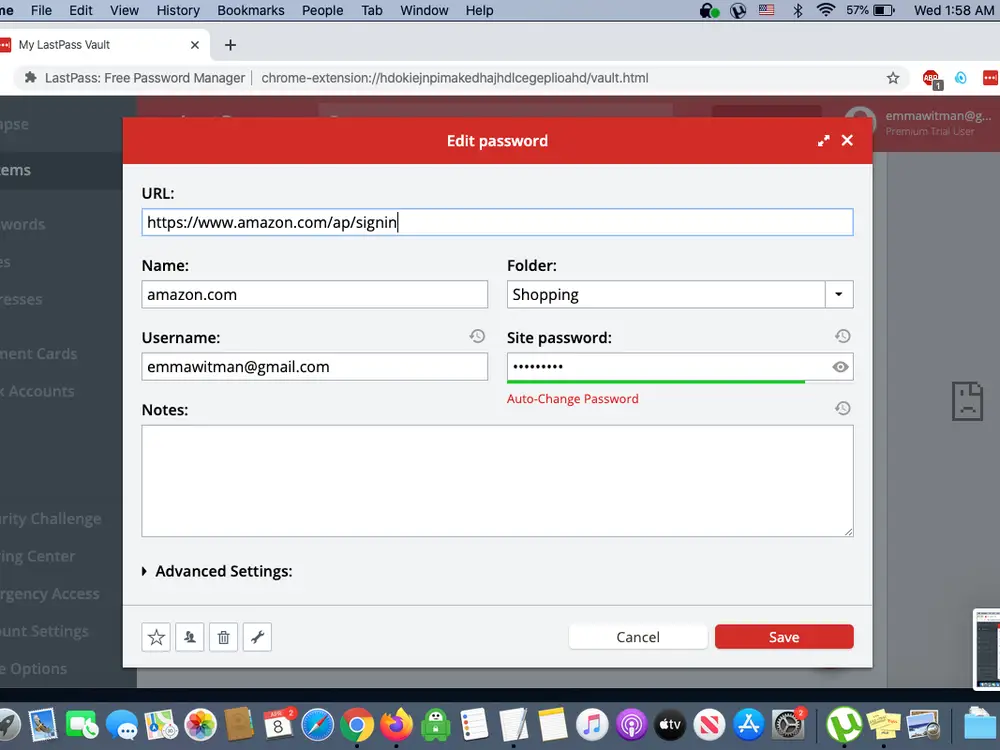
Down there in the “notes” section, I will put the challenge question and its answer. I always use the “generate random password” feature to generate a random password and use that as the answer to the challenge question. Good luck guessing that, hacker bitches.
All of your passwords are secure in your encrypted password wallet. Or are they?
LastPass was recently hacked, and a black hat used the credentials of an employee that was compromised in a phishing attack to gain access to and download their entire database of encrypted user files. I’m not blaming LastPass for that one- it could have happened to any company, and to their credit, at least they came clean and let everyone know.
This created two problems for LastPass users. Now that the black hats had the files, there are two ways that they can access them:
- They can try to brute force the master password for the file. This is where a strong master passphrase works to your advantage. If you are smart, as soon as you learn of the breach, you change the most important of your passwords (master password, followed by bank and email accounts, then others) before they get a chance to guess the master passphrase. By the time they have your passwords, you have already changed them and it won’t matter.
- Since LastPass encrypted file doesn’t encrypt the websites, only the login, password, and notes, the weakness here is that the black hat can do a targeted fishing attack similar to what was done to this Australian woman or this woman who was targeted by a man claiming to be a Chase fraud investigator. These attacks can be quite convincing.
To guard against someone compromising some or all of your passwords, you can use Multifactor Authentication (MFA). All MFA is, is a second way of ensuring that the person who is accessing an account is the authorized user. The most common of those is sending a code by SMS. You enter your password, then you get a prompt to enter a code or pin that’s sent to your phone number. After you type in the code, you’re in. Simple, right?
The problem is that SMS isn’t a secure way to perform MFA.
This is because SMS messages rely on the security of phone networks and phone companies. Both, sadly, are notoriously easy to access. While some text messages are encrypted user-to-user – think iMessages between iPhones or WhatsApp messages – SMS messages are in plain text form. Plain text messages are not encrypted between sender and receiver, so if attackers can intercept the message, they can read the content. Unfortunately, SMS messages are easy to intercept. Even Microsoft is advising people to stop using SMS as a method of MFA.
It’s time to start your move away from the SMS and voice Multi-Factor Authentication (MFA) mechanisms. These mechanisms are based on publicly-switched telephone networks (PSTN), and they are the least secure of the MFA methods available today. That gap will only widen as MFA adoption increases attackers’ interest in breaking these methods and purpose-built authenticators extend their security and usability advantages. Plan your move to passwordless strong authentication now – the authenticator app provides an immediate and evolving option.
Alex Weinert of Microsoft
Don’t rely on just a password. Don’t rely on one password. There are tons of scammers out there who want access to your stuff. Keep it as secure as you can make it.
The authenticator app still relies on you being in possession of your cell phone, and in my opinion creates a single point of failure- the loss of your phone, that places both the password wallet and the means of MFA in someone’s possession.
I don’t worry about the three letter agencies getting my stuff. If they want it, they are going to get it. They don’t need to steal my passwords, they aren’t going to spoof my phone, and they aren’t going to use my IOT devices to spy on me. You know what they are going to do? Present a national security letter to my bank, my employer, Google, my ISP, and anyone else they feel like, and the companies involved are going to tell them anything they want to know.
The purpose of the security I am writing about is protection from scammers who aren’t the government.
Still, there will be a future post on MFA, since this one is getting a bit long. On a side note, this series of posts represents my ongoing research into ways for securing my information. I tend to research and look into things that I am adopting. I figure that you can benefit from my research efforts.
4 Comments
PPM · January 10, 2023 at 7:20 am
I’ve heard to do the opposite on challenge questions. You don’t have to answer truthfully, but you should stick with human readable. Remember that it’s not always a computer accepting the challenge question, but often a person in a call center. If they’re told that the challenge answer is New York but it’s actually Delaware, they’ll realize something is up. If they’re told that the challenge answer is “well, mostly just garbled letters and numbers and punctuation”, they’ll probably accept that out of laziness, and you’ve just lost your account.
Divemedic · January 10, 2023 at 8:56 am
If I were going to do that, I would at least make sure that the answer doesn’t make sense. Call it the Biden Doctrine. For example:
In what state were you born?
Purple, because dogs don’t wear pants.
What is the name of your first pet?
23 because I have Chocolate Ice Cream
TRX · January 10, 2023 at 2:19 pm
That’s how I do it. I suspect the “challenge questions” primarily exist to collect more personal information from the user. I give random nonsense answers, though it would probably be better to use reasonable-sounding but incorrect ones.
All my logins, passwords, challenge answers, etc. are kept on paper, occasionally backed up by photocopying and putting one copie in my gun safe and the other off-site.
I don’t do internet on a phone, and a smartphone is too insecure for anything that needs a password anyway.
I’m not a Luddite; computer security was my job, years back. I maintain a minimal attack face. It might be convenient to do many things online, but I don’t even trust Linux desktops any more, much less Microsoft or fruit boxes. Smartphones are even worse.
AWA · January 10, 2023 at 11:39 am
There are a couple of different types of password managers out there. There are local password managers and then there are remote/cloud/shared managers.
Any password manager you use should have encrypted storage of your passwords. As an example, “Keeper” stores all records encrypted, it requires me to enter a password in order to decrypt my “vault”.
Nobody besides myself has the ability to decrypt that vault outside of capturing my decryption password. So if Keeper was compromised and the bad hats got all of the data, they would not be able to access my data without my password.
Local password storage is more secure IF you use it correctly. The downside is that if you loose your local password storage you’ve lost access to all your stored passwords.
Finally, consider using a physical security device such as an YubiKey. There are versions that will store passwords as well as provide authentication.
Comments are closed.